Capabilities
AlphaSOC identifies malicious behaviors, data exfiltration, and policy violations by analyzing structured telemetry across identity, cloud, application, network, and endpoint sources. The platform produces high-fidelity OCSF detection findings in real time and supports custom rule creation via Sigma and broad interoperability with your security stack.
Platform Coverage
AlphaSOC is data source agnostic and supports a wide range of environments and log formats:
| Category | Examples |
|---|---|
| Identity | Auth0, Entra ID, Okta |
| Cloud | AWS CloudTrail, AWS EKS, AWS Lambda, GCP Audit, Azure Activity |
| Application | GitHub, Google Workspace, Slack, Atlassian, Confluence, Jira, 1Password |
| Network | Cloudflare, Palo Alto Networks, Zscaler, Zeek, Suricata, Corelight |
| Endpoint | CrowdStrike, Microsoft Defender, SentinelOne |
Telemetry is normalized to OCSF upon ingestion and analyzed consistently across all supported formats. For the full list of supported data origins, see the Data Origins page.
Detection Categories

AlphaSOC combines behavioral analysis, threat intelligence, and active scanning to identify both known and novel threats. Detection categories include:
- Command and control (C2): Beaconing, callbacks, domain fluxing.
- Data exfiltration: DNS tunneling, ICMP tunneling, anomalous uploads.
- Cryptomining: Traffic to mining pools or abused VPS infrastructure.
- Phishing and malware: Lookalike domains, newly registered infrastructure, Certificate Transparency monitoring.
- Policy violations: Potentially unwanted programs, outdated browsers, proxy avoidance tools.
- Protocol abuse: Use of cleartext protocols (e.g. FTP, Telnet) and atypical port usage (e.g. SSH over port 443).
- Anonymizing circuits: Tor, I2P, Freenet.
- Low-prevalence destinations: Domains or IPs contacted by only one host across all AlphaSOC deployments, often a hallmark of targeted campaigns.
- Identity threats: Unusual logins, permission escalation, credential misuse across identity providers and application platforms.
- Configuration drift: Changes toward insecure states, bulk exports, public sharing of sensitive resources.
Each detection is scored for severity based on risk and confidence using six dimensions of analysis, and enriched in real time with threat intelligence and contextual metadata to support informed triage. For a detailed technical breakdown of the scoring pipeline, see Architecture: Six Dimensions of Scoring.
Anomaly Detection

Beyond rule-based detection, AlphaSOC continuously analyzes telemetry for behavioral outliers and environmental deviations:
- Time-based anomalies: Unexpected session durations, beacon intervals, or access times.
- User and identity outliers: Unusual logins across application platforms, sudden permission changes, or rare user-agent strings.
- Resolver and network deviations: New outbound DNS resolvers or rare ASNs.
- Global rarity: Destinations queried by only one host across the entire customer base.
The system highlights behavioral deviations that signal stealth operations such as command-and-control beaconing, credential misuse, or lateral movement, commonly seen in red teaming and targeted APT activity.
Custom Detections with Sigma
AlphaSOC supports detection-as-code using the Sigma rule format. Threat hunters deploy custom rules via version control (e.g. GitHub) and CI/CD pipelines without translating to vendor-specific query languages.
- Extend managed detection logic with environment-specific rules.
- Tune severity and scoring per rule.
- Create private, shareable, or community-based rules.
- The Sigma community repository contains thousands of rules for Windows, macOS, Linux, cloud platforms, and applications.
Rules are processed alongside managed detections (aligned to MITRE ATT&CK) and mapped to the same OCSF detection finding pipeline.
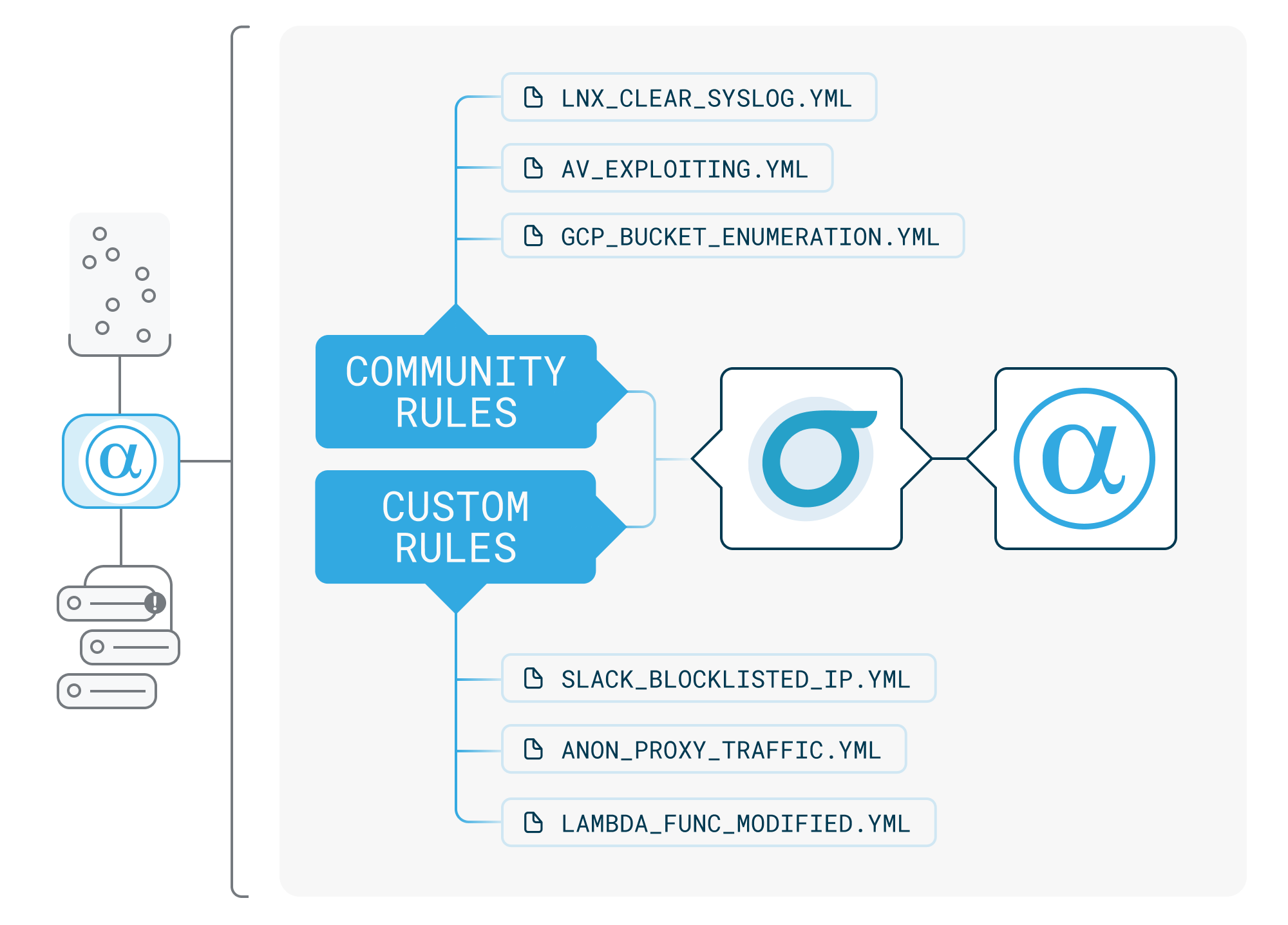
Managed Detections
AlphaSOC maintains a library of managed detections aligned to MITRE ATT&CK, covering known threat actor tactics, techniques, and procedures. Managed detections are continuously updated and require no configuration. They run alongside custom Sigma rules within the same scoring pipeline.
For a complete list of managed detections, see the Detections page.
Integration and Finding Delivery
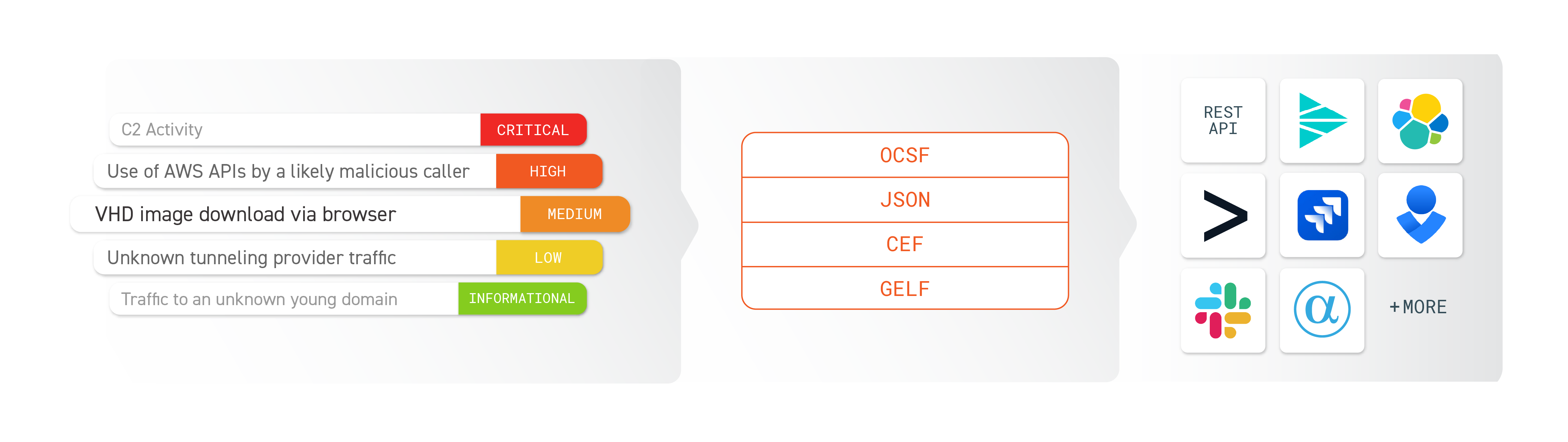
OCSF detection findings are delivered to your existing security stack:
| Destination Type | Examples |
|---|---|
| SIEM | Google SecOps, Microsoft Sentinel, Splunk ES |
| SOAR | Cortex XSOAR, Splunk SOAR, Tines |
| Data Lake | Databricks, Security Lake, Snowflake |
| Ticketing | Jira, ServiceNow, Linear |
| Agentic AI | Claude, Copilot, OpenAI |
Findings are available via REST API (pull or push), native integrations, and the AlphaSOC Web Console. Supported formats include OCSF and JSON, with custom formats available on request.
Summary
AlphaSOC provides:
- Detection across identity, cloud, application, network, and endpoint telemetry sources.
- Behavioral and anomaly detection for novel, low-prevalence threats.
- Managed detections aligned to MITRE ATT&CK, continuously updated.
- Detection-as-code with Sigma rules deployed via version control and CI/CD.
- Integration with SIEM, SOAR, data lake, ticketing, and agentic AI platforms.
For a technical breakdown of the detection pipeline, scoring dimensions, and deployment models, see the Architecture page.
Need help integrating AlphaSOC into your environment? Contact us.