Architecture
AlphaSOC is a dedicated threat detection engine that ingests telemetry from identity, cloud, application, network, and endpoint sources, normalizes and enriches it, and applies a patented scoring stack to detect threats. This page provides a system-level overview of the AlphaSOC architecture and how its components operate across deployment models.
Detection Pipeline
AlphaSOC processes telemetry through a five-stage detection pipeline:
- Ingest. Load cloud, application, network, and endpoint logs from any source. AlphaSOC supports structured telemetry in OCSF, JSON, Syslog, CSV, and other formats. No agents or sensors to deploy.
- Normalize. Map all data fields to OCSF for consistent analysis. Ingested data is normalized into a unified schema with standardized identity, protocol, and timestamp fields, enabling portable analytics regardless of the original log source.
- Enrich. Add threat intelligence from 70+ sources and prevalence data to each event. AlphaSOC houses 1M+ live, curated indicators. Events are also enriched with IP geolocation, ASN data, and DNS resolver fingerprinting.
- Score. Evaluate events using a patented scoring stack that combines custom Sigma rules and managed AlphaSOC detections aligned to MITRE ATT&CK. The scoring stage applies six dimensions of analysis (described below) to reveal both known and unknown threats.
- Alert. Escalate OCSF detection findings to your security team for investigation and triage.
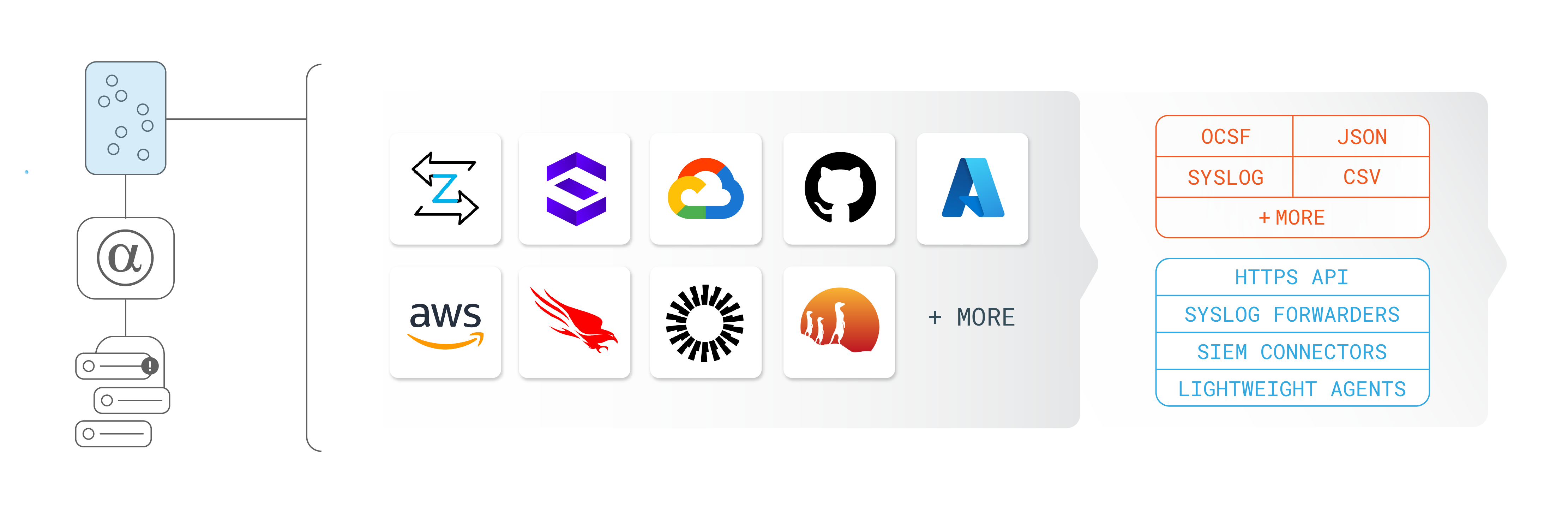
For the full list of supported telemetry sources and platforms, see Capabilities: Platform Coverage.
Six Dimensions of Scoring
The Score stage applies six dimensions of analysis to each event:
- Active fingerprinting: Through an anonymizing proxy layer, AlphaSOC actively scans destinations observed in telemetry to identify C2 infrastructure in real time. This includes evaluating the infrastructure behind suspicious API callers and login sources in cloud, application, and identity logs.
- Reputation scoring: Using third-party APIs (e.g. sandboxing engines and threat blocking providers), AlphaSOC gathers live reputation data for observed entities. This covers network destinations, source IP addresses in cloud audit logs, and callers interacting with identity providers and applications such as Okta, GitHub, and Slack.
- Prevalence analysis: AlphaSOC measures how common or rare an observed behavior is, both within your environment and across all AlphaSOC customer environments. This surfaces first-time API calls, unusual administrative actions, rare network destinations, and atypical configuration changes that stand out against local and global baselines.
- Time series modeling: AlphaSOC baselines activity to detect anomalous patterns over time. This includes network beaconing and exfiltration patterns, login spikes, bulk API call bursts, and abnormal data access volumes across cloud and application platforms.
- Feature classification: AlphaSOC identifies structural characteristics that indicate malicious intent. For network telemetry, this includes DNS tunneling, DGAs, and protocol misuse. For cloud and application telemetry, this covers configuration drift toward insecure states, permission escalation patterns, and data exposure indicators such as bulk exports or public sharing.
- Intelligence correlation: AlphaSOC matches observed activity against curated and third-party threat intelligence feeds updated hourly. This applies across all telemetry sources, from network traffic to source IPs in cloud API calls, identity provider logins, and application events.
Correlation and Escalation
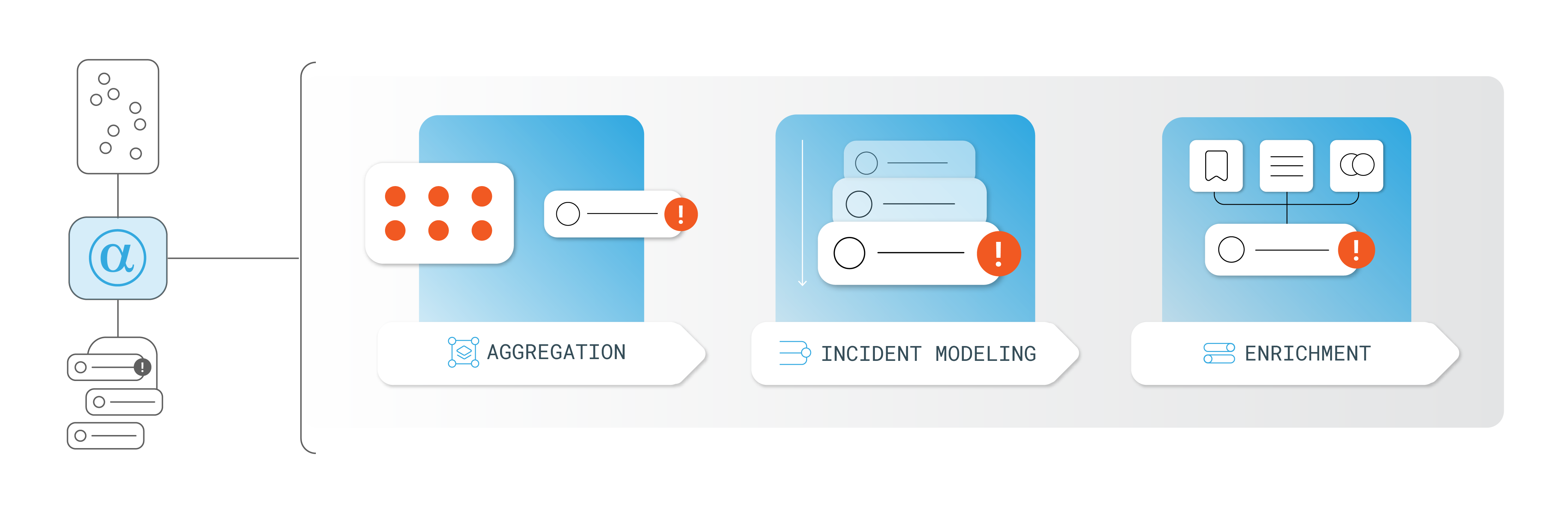
After individual events are scored, AlphaSOC applies correlation logic across identities, endpoints, and timeframes to produce higher-confidence results:
- Related detections are aggregated into composite OCSF detection findings.
- Multi-stage activity is modeled to surface coordinated attack patterns.
- Events are enriched with user and asset context to reduce noise and prioritize actionable outcomes.
This pipeline helps solve the patient zero problem by surfacing threats that do not yet have IOCs. Behavioral anomaly detection highlights unusual logins, access patterns, configuration changes, and rare infrastructure. Related events are automatically correlated into actionable OCSF detection findings.
For details on specific detection categories and anomaly modeling, see the Capabilities page.
Deployment Models
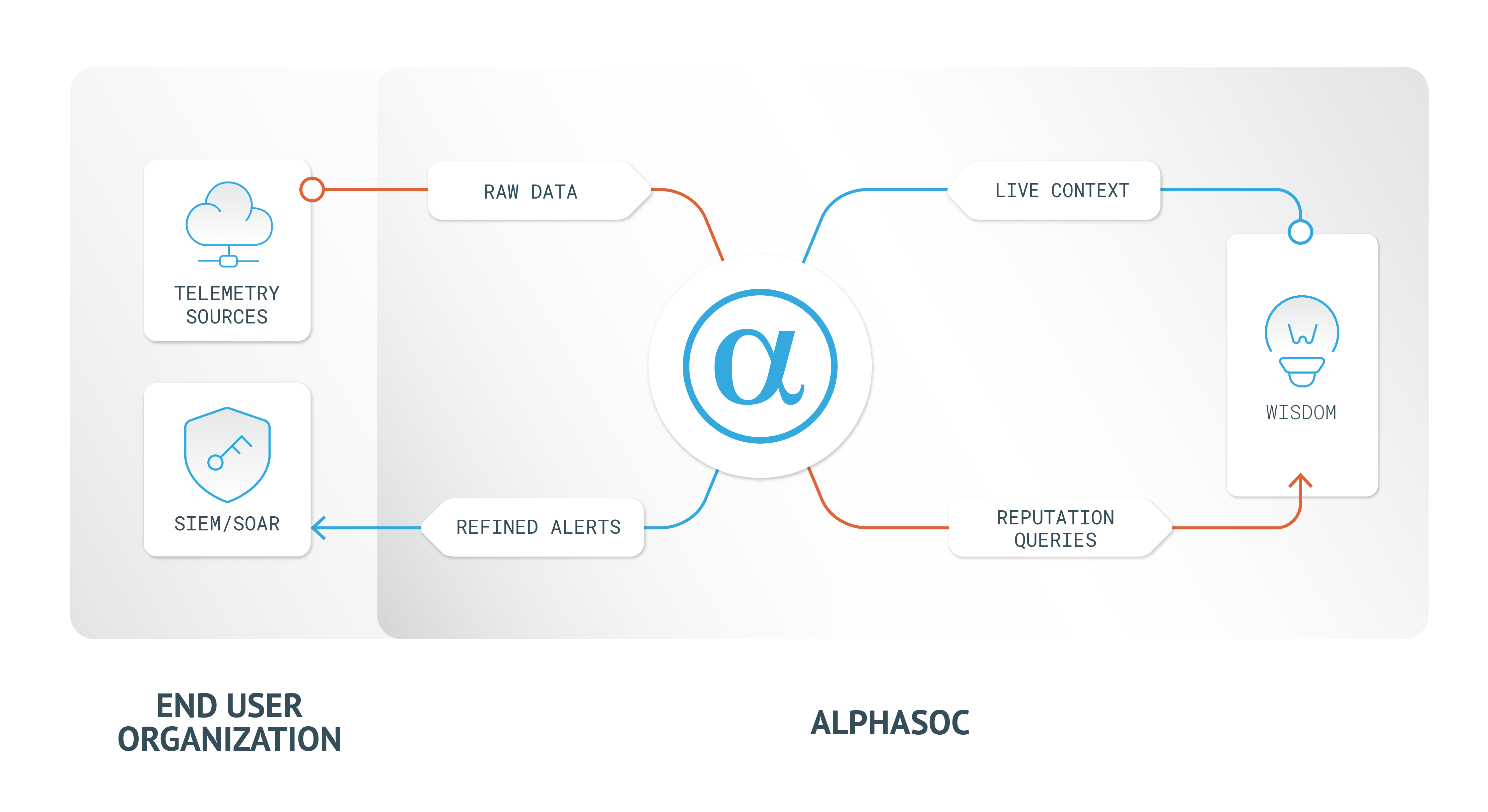
Cloud
In the SaaS model, customers forward telemetry via HTTPS. AlphaSOC performs real-time analysis and delivers OCSF detection findings:
- Multi-tenant analytics engine optimized for speed and scale.
- Output available via API or native integrations.
- Customers retain full control over log forwarding and routing.
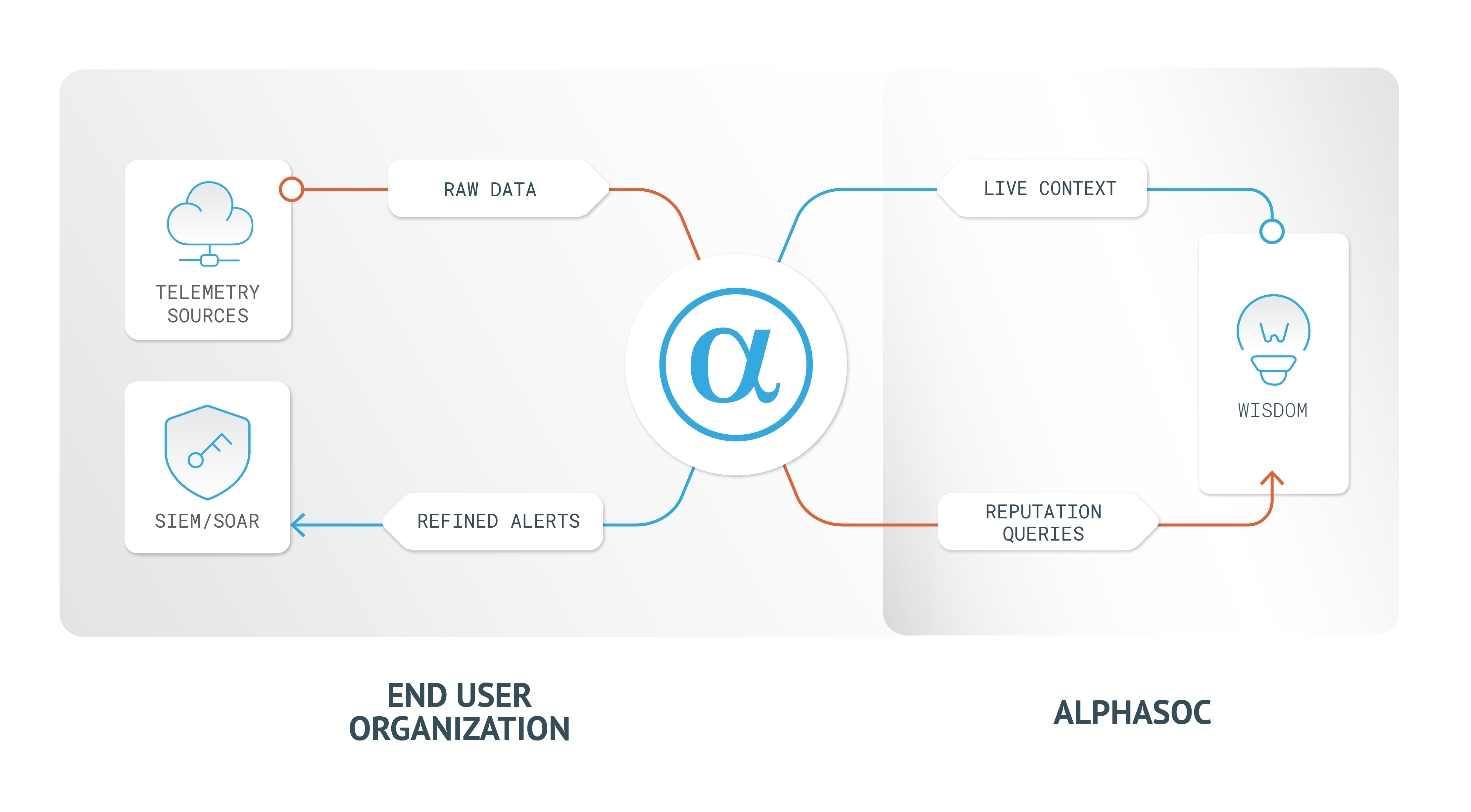
On-Premise
AlphaSOC also supports local processing in customer-controlled environments. All raw telemetry is handled internally, with only metadata sent to the Wisdom API for threat enrichment:
- Suited for air-gapped, regulated, or privacy-sensitive deployments.
- No raw data leaves the environment.
- Local web interface for configuration and finding review.
Summary
AlphaSOC architecture supports:
- A five-stage detection pipeline: Ingest, Normalize, Enrich, Score, Alert.
- Six dimensions of scoring using a patented scoring stack.
- Correlation and escalation logic to produce high-confidence OCSF detection findings.
- Cloud and on-premise deployment models.
For supported platforms, detection categories, custom Sigma rules, and integration destinations, see the Capabilities page.
Questions? Contact support@alphasoc.com.